Ask an Expert
Planning the right solution requires an understanding of your project's security goals. Let Kingston's experts guide you.
Your web browser is out of date. Update your browser now for better experience on this site. https://browser-update.org/update-browser.html


Daniel Döring is Managing Director of EgoMind and is responsible for the operational business of the German software development provider. He is also Managing Director at smart2success GmbH where he oversees product development, information technology, and technology partnerships at the risk/project/change management provider. He draws on his experience and knowledge of areas including IT security and software development, which he has gained since 2004.
Previously, he was responsible for the development and expansion of the product portfolio, support, pre-sales, consulting, academy, and technology partnerships at the IT security manufacturer EgoSecure.
USB storage drives continue to be widely used, especially in the era of remote work. Employees value having access to their data anytime, anywhere. Despite the availability of cloud storage and collaboration tools, the reliance on external data storage remains significant and necessary. People often feel more secure when their sensitive data is stored on devices under their control and within close physical reach. However, these external storage devices are sometimes lost or stolen, posing a risk of data breach. Therefore, it is crucial to always encrypt data stored on these storage devices.
Compared to their software-encrypted counterparts, hardware-based encrypted drives like IronKey offer many benefits, such as faster read/write speeds and low usage overhead. This is due to their inherent encryption functionality, which does not require any encryption/decryption software to be installed on a host system to access the drive’s data.
Are hardware-encrypted USB drives secure? The most common commercial encryption technology is AES 256-bit. This is considered secure by NIST, which invented the widely used AES encryption standard. Ordinary users cannot bypass this encryption, and even hackers or targeted attackers typically do not invest the effort required to crack the actual encrypted cyphertext. Instead, attackers are more likely to exploit vulnerabilities in user behavior through social engineering attacks or the security implementation of storage drives.
User vulnerabilities include weak or guessable passwords caused by user fatigue of managing too many complex passwords. What is worse, however, is that security vulnerabilities can often exist within applications or drives. Attackers may attempt to spy on passwords during input or electronically attempt to manipulate the drive authentication process to gain access to the encrypted data.
This creates a problem for users of such drives—how can they trust the manufacturer to implement proper safeguards and security to ensure that data is protected against hackers and attackers who may find the drive or, even worse, have stolen it?
To ensure the security of the leading enterprise-grade IronKey Vault Privacy 50 series, Kingston Technology arranged for penetration tests to be performed by third-party experts who simulated hacking attempts to identify and address vulnerabilities rather than exploit them for criminal purposes. Pen testing is one of the best tools in cybersecurity to provide confidence in a device or software and ensure that the product’s security design is robust.
Enhanced data security:
Hardware encryption ensures that the data stored on the VP50-series drives is protected at rest and in transit. It uses a dedicated secure microprocessor embedded in the drive, making it resistant to software-based attacks as well as password guessing—this is known as BadUSB where the drive keeps track of invalid passwords and ultimately crypto-erases its contents to prevent access to the data. This added layer of security reduces the risk of unauthorized access and data breaches.
Ease of use:
Hardware-encrypted VP50 drives are user friendly. They include built-in secure software authentication that runs without needing installation on a system, making it convenient for users to unlock and access their encrypted data. This eliminates the need for the complex encryption setups usually required with software encryption, simplifying the data protection process. As a result, the ease of using hardware-encrypted drives ensures that employees will be less likely to turn to insecure workarounds.
Compliance with security standards:
Many industries and organizations have specific security and compliance requirements such as GDPR, which requires strong encryption of data. Hardware-encrypted IronKey drives often meet or exceed these standards, which includes FIPS 197 certified AES-256 bit encryption in XTS mode. FIPS 197 is a lab-tested certification that verifies the encryption is properly implemented as designed by NIST.
Protection from malware:
Hardware encryption is performed entirely within the USB drive itself, meaning that encryption keys never leave the drive and are not exposed to the attached computer’s memory where they can be snooped upon, retrieved from swap or hibernation files, and discovered. This protects the drive’s data from malware that may be present on the host system trying to intercept the encryption keys.
Increased performance:
Hardware encryption is faster than software encryption methods, as it offloads the encryption and decryption tasks to the dedicated secure microprocessor within the USB drive. This results in faster data transfers and improved overall performance compared to software-based encryption solutions, which use host PC resources.
Trusted vendor:
The key benefit of successfully passing pen testing by an independent third-party is to assure customers that the drive is engineered to high security standards and can be trusted as a data protection device.
It is important to note that while pen-tested, hardware-encrypted USB drives provide significant security advantages, they should still be used in conjunction with other security measures, such as strong passwords, regular data backups, and secure data-handling practices, to ensure comprehensive data protection. In addition, enterprises need to implement good data security hygiene so all employees follow guidelines to properly safeguard sensitive information.

The established professional penetration testing team from SySS GmbH in Germany subjected Kingston Ironkey Vault Privacy 50 series (Type-A & Type-C®) drives to penetration tests, specifically focusing on user authentication and key handling within the user software.
The penetration testing was successfully completed without discovering any vulnerabilities, leading to Kingston IronKey receiving an Approved Security certificate from SySS GmbH.
With a longstanding reputation and strong trust, Kingston IronKey leads the way in hardware-encrypted USB drives, providing customized support tailored to your business requirements. Their exceptional "Ask an Expert" team ensures personalized advice that precisely aligns with your environment and unique needs.
#KingstonIsWithYou #KingstonIronKey
Was this helpful?

Planning the right solution requires an understanding of your project's security goals. Let Kingston's experts guide you.

How EU regulations impact data storage, cloud usage, and compliance strategies.

David Clarke covers encryption, superuser safeguards, vulnerability management, and training.

We discuss NIS2 and DORA, and how organizations can turn compliance into an opportunity.
We discuss the shifts in how organizations are storing and encrypting sensitive data.

Security expert David Clarke explains the key differences between NIS and NIS2.

Security expert David Clarke explains who will be affected by the NIS2 directive and how.

Remembering to back up frequently can evade even the most experienced tech enthusiast. We’ll cover some simple tricks to ensure you can easily back up regularly.

For creatives producing content for high-profile clients, encrypted storage can secure your important files and help you fulfil your security responsibilities.

There are two main types of encryption - software encryption and hardware encryption.

How to maximize your online security by taking steps to protect your presence.

You can access encrypted data on an iPad or iPhone with Kingston USB Flash drives. Here’s how.

Encrypted USB flash drives keep your private data safe, but how do they work?

Learn how to erase SSDs, hard drives or any other storage mediums so that the data is really gone forever.

Learn how to erase SSDs, hard drives or any other storage mediums like a security professional.
No products match your current filter selection. Try adjusting your filters to explore more options.

Looking for improved data security & need to know what is encryption? Kingston covers the basics.

Hardware, not software-based password protection, is the best way to protect files and drives.

Secure important personal and private information on a PC with a hardware encrypted SSD.

Most IronKey and Kingston secure USB flash drives are FIPS 140-2 Certified.

A look at how companies manage their systems when cloud computing is unavailable.

Your guide to EU data sovereignty, risks, and secure data storage strategies.

Discover how encrypted USB drives protect your data, and which type fits your needs.

Learn the right way to protect data and prepare it for safe reuse or recycling.

Breaches remain a major threat. Explore the need of comprehensive cybersecurity measures.

Here is a list of USB security features to consider for data protection.

Learn what the 3-2-1 data backup method is and why it is your best defense against ransomware.

Learn data security best practices with Dr. Vynckier, and the importance of offline backups.

David Clarke covers encryption, superuser safeguards, vulnerability management, and training.

Learn how Kingston IronKey's solutions helped EgoMind enhance their data security hygiene.

The differences between SSD classes lies in two components; the processor and the NAND memory.

We discuss NIS2 and DORA, and how organizations can turn compliance into an opportunity.

We discuss the shifts in how organizations are storing and encrypting sensitive data.

Kingston examines how to secure sensitive files with the increasing vulnerability of email.

Learn how Kingston IronKey hardware-encrypted solutions supports NIS2 Directive compliance.

Kingston IronKey has hardware options to protect small and medium businesses against cybercrime.

FIPS 140-3 Level 3 is certified by the world-leading agency NIST as the apex of encryption.

Questions to ask when seeking the right SSD for your organization’s data center.

Our infographic showcases the differences between software and hardware-based encryption.

2023 has been a year full of challenges and innovations. But what will 2024 bring?

Learn about two methods that give SMBs superior resilience vs. ransomware: encryption & backups.

In this whitepaper, we explain how to enforce a DLP strategy, while allowing USB drive use.

Enterprise-grade and military-grade digital security: two high standards with different requirements.

Learn how hardware encryption can protect a travelling lawyer’s confidentiality with secure file storage.

Hardware-encrypted Kingston IronKey drives protects organizations’ data on the move.

Bring Your Own Device (BYOD) policy is tricky for employers. How to balance security & convenience?

How do encrypted drives improve cybersecurity and compliance for finance companies? Kingston explains.

DLP offers tools for network admins to protect sensitive data from cybercrime and negligence.

A look at how the requirement of data encryption can be key to any organization's security strategy.

How can we bolster network security with remote working and international travel so common now?

Invest in encrypted drives so that if they are lost or stolen you are not on the hook for legal fees which can be more expensive.

Discover why national security agencies trust Kingston IronKey to protect their data.

A company’s IT specialists should be expected to add data security to the PCs of remote workers.
Kingston’s three key practices for a robust DLP for businesses handling sensitive data.

You can read and write to an encrypted USB flash drive with an iPad or iPhone with the right adaptor. Here’s how.

Learn why hardware encryption beats software encryption for law firm data protection.
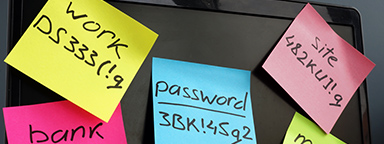
Passphrases are superior to complex passwords for keeping data secure, with many powerful benefits.

A brief explaining the purpose and types of data security software available.

HIPAA requires healthcare organizations to always keep patient data safe, including in transit.

This requires encryption of sensitive data, appointing a Security Officer, cyber security programs and policy adoption.

Kingston IronKey encrypted USBs are a security consideration for organizations of all sizes.

We compare unencrypted and encrypted USB drives and explain how to keep data secure!

Learn how Kingston IronKey is protecting the intellectual property with customization.

Discover why Kingston IronKey is the go-to solution for protecting financial services data.

Learn how Kingston IronKey is securing the military operations’ data.

How can you get your organization to use encrypted drives and make them part of your security policy? Here are some tips.

Learn how Kingston IronKey is protecting the telecoms industry's data using encryption.

Encryption is an incredibly helpful option for creatives to protect their clients’ important files.

Kingston IronKey encrypted USBs: a small but important part of any organization’s security strategy.

Kingston IronKey can help mitigate data loss resulting from the rise in lost electronic devices.

In this eBook, we explore how encrypted USB drives have become a key tool in keeping data secure.

How to use your IronKey Vault Privacy 80 External SSD: set password, connecting to a PC and more.

Organizations are considering data security options to protect against private mobile data breaches.

Discover how Kingston IronKey is protecting the sensitive data of the finance sector.

Here is how Kingston IronKey helped protect the sensitive data of the Energy industry.

We explore our KingstonCognate experts’ thoughts on cyberthreats and cybersecurity challenges.

Software based encryption can be disabled by the user. This can lead to fines and legal fees if the drive is lost.

We explore Tomasz Surdyk's thoughts on how all entities can stay secure in the digitized world.

Don’t plug any USB drives into your computer if you don’t know exactly where they came from.

Protection data on the move with superior hardware-based Advanced Encryption Standard (AES) 256.

What we learned from Kingston’s experts and tech influencers on work-from-home enablement Twitter chat.

There are benefits to using both cloud storage and hardware-based encryption.

We explore the top 12 tips small and medium size enterprises can take to enhance cybersecurity.

We’ve examined several factors using unique research to identify what may impact markets globally in 2022.

2021 has been a year full of challenges and innovations. But what will 2022 bring?

Prof. Sally Eaves shares her thoughts on the SME cybersecurity landscape and the need for education & support.

Bill Mew shares his thoughts how the largest security challenges need commitment from the boardroom.

Rob May shares his thoughts on how close we are to edge computing and the security it requires.

Write your diary digitally with a password protected, cloud backup solution.

The pandemic has increased internet traffic which has placed importance on the role of data centers.

The use of DLP software, VPNs, encrypted SSDs, and USBs will help mitigate some risks of remote working.

Cameron Crandall of Kingston helps you self-evaluate the need to move to your server storage solution to NVMe.

There are many advantages to using a dedicated hardware encryption processor in USB flash drives.

What will 2021 bring in tech and trends? What do our KingstonCognate members and industry experts predict for the future?

Cyber security and data privacy are everyone’s responsibility. What are the key considerations?

Learn why the future of business depends on SSD-enabled SDS, and how SSD fits into software-defined storage solutions.

Kingston & Matrix42 partnered to give optimal endpoint security solution in multiple sectors to mitigate risks.

Organizations must consider revenue, profit, and risk equally in order to mitigate data security & cyber security risks. In this article, industry expert Bill Mew provides an insight into this topic.

What do industry experts think has changed since the introduction of GDPR?

Data centers should be using server SSDs. There are many benefits over client drives and costs have come down.

NVMe is now the standard protocol for SSDs to empower data centers and enterprise environments.

SDS hasn’t lived up to its hype but now that NVMe is more affordable the commodity hardware is ready to deliver.

Choosing the right SSD for your server is important since server SSDs are optimized to perform at a predictable latency level while client (desktop/laptop) SSDs are not. These difference result in better uptime and less lag for critical apps and services.

Cloud and on-premise data center managers can learn a lot from supercomputing.

To work from home you need a good workspace for your PC, the right conferencing gear, and a secure connection.

What strategies can organizations use to best secure customer data in a post-GDPR world with the ever-evolving nature of cyber security threats? Kingston pooled the knowledge of some of the UK’s most experienced commentators in cyber security to discuss how data protection has changed since the introduction of GDPR.

This whitepaper demonstrates how using Kingston Technology’s Data Centre DC500 SSDs can reduce your overall capital and licence costs by 39%.

Data Center 500 Series SSDs (DC500R / DC500M) – Consistency, predictability of Latency (response time) and IOPS (I/Os Per Second) performance.

You already know that remote working is a business enabler. But the challenges posed to your network security and compliance with GDPR are too big to ignore.

How to enable and disable Microsoft’s BitLocker eDrive feature to leverage hardware encryption on your Kingston SSD

The recent WannaCry ransomware made global headlines infecting and alerting everyone from government, healthcare, communication providers, automotive companies to corporations and the general public of their vulnerabilities.

Overall, Kingston / IronKey Encrypted USB Drives prove to be the best solution in reliability, compatibility and security for portable data protection solutions.

End-to-End Data Protection protects customer’s data as soon as it is transferred by the host system to the SSD, and then from the SSD to the host computer. All Kingston SSDs incorporate this protection.

Some of Kingston and IronKey's Secure USB Flash drives are powered by partners, licensed technology, or services.

HPC can require massive amounts of data. SSDs consume a fraction of the power of their spinning disk.

Kingston datacenter SSDs provide excellent resiliency to protect sensitive data in OLTP workloads.

This program offers the options most frequently requested by customers, including serial numbering, dual password and custom logos. With a minimum order of 50 pieces, the program delivers precisely what your organization needs.
256-bit AES hardware-based XTS block cipher mode encryption is used in DT 4000G2 and DTVP 3.0.

Everyday working life has changed radically and so have traditional ways of working: thanks to mobile storage media, we can access our data practically at any time from any location, and can work on our data wherever we are.

Case in point, Heathrow Airport in London (October 30, 2017) uses Unencrypted USB Drives for its non-cloud storage. Unfortunately, they were not standardized on Encrypted USB drives. Their lack of implementing proper standards in data security / data loss protection with encrypted USB storage has now cost the EU a major breach of confidential and restricted information.

Linus breaks down hardware encryption making sure your files are safe and secure, especially when you're on the go. Make sure your portable storage is also safe and encrypted with Kingston Encrypted USB drives.

Storage can be the most challenging component for VDI performance.

Testing is a cornerstone of our commitment to deliver the most reliable products on the market. We perform rigorous tests on all of our products during each stage of production. These tests ensure quality control throughout the entire manufacturing process.

NVMe (Non-Volatile Memory Express) is a communications interface and driver that defines a command set and feature set for PCIe-based SSDs with the goals of increased and efficient performance and interoperability on a broad range of enterprise and client systems.